|
IN THIS ISSUE
- Cybersecurity is a Big Deal for Small Businesses
- Partner Spotlight: ConnectSafely
- Federal Spotlight: C^3 Voluntary Program
- Updated Stop.Think.Connect. Toolkit
Cybersecurity is a Big Deal for Small Business
Cyber
attacks against big businesses tend to get a lot of attention. Media
extensively covered the incidents involving AT&T in 2010 (over
14,000 emails stolen), Sony in 2011 (over 77 million credit card numbers
stolen), and Target in 2013 (over 40 million credit card numbers
stolen).
While big businesses may get all the press, small businesses are not immune from a cyber attack. The 2013 Verizon Data Breach Investigations Report found that over 40 percent of all data breaches occurred in companies with less than 1,000 employees.
Small businesses may be more vulnerable to attacks because cyber criminals assume they have weaker network security. The 2012 Small Business Study,
conducted by the National Cyber Security Alliance and Symantec, found
that 83 percent of small businesses do not have written cybersecurity
plans, with 11 percent of small businesses reporting that they have no
one responsible for cybersecurity.
With
small businesses increasingly dependent on the Internet to conduct
business, the effect of cyber incidents can be devastating. So how can
small businesses protect themselves? It helps to start with the basics.
Follow these tips from the Stop.Think.Connect. Small Business Tip Card:
- Keep a clean machine. Use and regularly update antivirus and antispyware software on all computers.
- Connect safely. Secure your Internet connection by using a firewall, encrypting information, and hiding your Wi-Fi network.
- Safeguard information.
Establish security practices and policies to protect sensitive
information; educate employees and hold them accountable to the Internet
security guidelines and procedures.
- Focus on people.
Require that employees use strong passwords and regularly change them.
Educate your employees on the importance of safe cybersecurity
practices.
Additional government resources specifically for small businesses include:
- The Federal Communications Commission (FCC) Small Biz Cyber Planner,
a tool for businesses to create custom cybersecurity plans. Developed
in partnership with the Department of Homeland Security (DHS), the
National Cyber Security Alliance, and private sector partners, the Small
Biz Cyber Planner includes information on cyber insurance, advanced
spyware, and how to install protective software.
- The U.S. Chamber of Commerce Internet Essentials for Business 2.0 guide
for business owners, managers, and employees. The guide focuses on
identifying common online risks, best practices for securing networks
and information, and what to do when a cyber incident occurs.
- The U.S. Small Business Administration Cybersecurity for Small Business
training course covers the basics of cybersecurity and information
security, including the kind of information that needs to be protected,
common cyber threats, and cybersecurity best practices.
Another
helpful resource for businesses looking to improve their cybersecurity
and manage their cyber risks is the SANS Institute’s Top Critical Security Controls for Cyber Defense.
For each security control listed, SANS recommends quick actions to more
advanced cyber activities to help protect against cyber attacks and
intrusions.

Partner Spotlight: ConnectSafely Hosts Safer Internet Day
ConnectSafely
is a non-profit Internet safety organization that hosted the first U.S.
observance of Safer Internet Day on February 11, 2014. Safer Internet
Day is observed around the world as a day to promote responsible use of
online technology. The keystone event was a panel presentation with
representatives from Facebook, Google, Yahoo, and Twitter, along with
Representative Chuck Schumer (D-NY), talking about responsible online
activities on their companies’ social media platforms such as Instagram,
YouTube, and Tumblr.
At this event, ConnectSafely distributed its newly updated Parents Guide to Instagram,
which includes information about the application’s new direct message
feature. The guide includes background information about Instagram, how
to share pictures responsibly, and what to do if someone harasses you.
This guide is part of series on social media, including the Parents
Guide to Facebook and Parents Guide to SnapChat. Visit the ConnectSafely Parents Guide page for more resources. |

Federal Spotlight: C^3 Voluntary Program
The
way we connect and interact online using the modern conveniences of a
digitally connected world is not only a part of our individual lives:
cyber systems and networks also fuel our nation’s critical
infrastructure. This includes the broadband networks beneath us and the
wireless signals around us, the local networks in our schools,
hospitals, and businesses, and the massive grids that power our country.
Critical infrastructure is the lifeblood of our Nation’s security,
economy, and health. As a result, it is a prime target for attack from
those seeking to cause our country harm.
To
help protect against these types of attacks against our nation’s
critical infrastructure, in February 2013, President Barack Obama signed
Executive Order 13636: Improving Critical Infrastructure Cybersecurity
(EO 13636). Through this Executive Order, the President acknowledged
that the “cyber threat to critical infrastructure continues to grow and
represents one of the most serious national security challenges we must
confront.”
EO
13636 included several activities for the Federal Government to
complete by February 2014. It tasked the National Institute of Standards
and Technology (NIST) to develop a Cybersecurity Framework (the
Framework) to provide industry with a set of guidelines to help improve
their cyber risk management. To support the use of this Framework, EO
13636 asked DHS to develop a voluntary program. This program – the
Critical Infrastructure Cyber Community Voluntary Program, or C^3
Voluntary Program (pronounced “C-Cubed”) – launched on February 12,
alongside the final Framework.
While
DHS leads the national effort to protect critical infrastructure and
safeguard our Nation’s cyber resiliency, the Department cannot do it
alone. The C^3 Voluntary Program understands that emerging cyber threats
require the engagement of our entire society—from government to the
private sector and to members of the public. The C^3 Voluntary Program
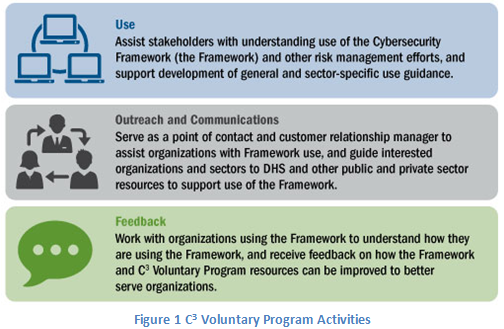
will focus on three primary activities: helping stakeholders understand
and use the Framework, conducting outreach and communications, and
encouraging feedback around program resources.
|
Currently,
DHS has many resources available to industry for their cyber risk
management efforts. The C^3 Voluntary Program aims to serve as the point
of coordination within the Federal Government to help industry be aware
of and use these existing resources.
With
the Framework’s recent release, the C^3 Voluntary Program will spend
the next year working with partners to develop Framework implementation
guidance for all 16 critical infrastructure sectors, and for small and
medium sized businesses.
Those looking to participate in the program now can visit its web pages at www.dhs.gov/ccubedvp and www.us-cert.gov/ccubedvp.
At the US-CERT website, users can learn more about existing government
resources or download a Cyber Resilience Review assessment to complete
for their organization. The site will be updated as more resources and
guidance become available.
Coming Soon: Updated Stop.Think.Connect. Toolkit
The
Stop.Think.Connect. Campaign is excited to announce an updated version
of the Campaign Toolkit, which will be introduced at the annual RSA
Conference, February 24-27.
The updated Toolkit offers Friends and partners of the Campaign:
- An updated and engaging format, enabling
organizations to edit and customize content for use in their own
presentations and engagement activities
- New information about cyber education
- New section focused on mobile safety
- Updated facts and figures
This
Toolkit update would not be possible without all the great feedback
from Campaign Friends and National Network and Cyber Awareness Coalition
partners. The updated Toolkit will be available at www.dhs.gov/stopthinkconnect in the Spring. | 

No comments:
Post a Comment